- Home
-
CWE-287: Improper Authentication
Weakness ID: 287Vulnerability Mapping: DISCOURAGED This CWE ID should not be used to map to real-world vulnerabilities
Abstraction: Class Class - a weakness that is described in a very abstract fashion, typically independent of any specific language or technology. More specific than a Pillar Weakness, but more general than a Base Weakness. Class level weaknesses typically describe issues in terms of 1 or 2 of the following dimensions: behavior, property, and resource.View customized information:For users who are interested in more notional aspects of a weakness. Example: educators, technical writers, and project/program managers. For users who are concerned with the practical application and details about the nature of a weakness and how to prevent it from happening. Example: tool developers, security researchers, pen-testers, incident response analysts. For users who are mapping an issue to CWE/CAPEC IDs, i.e., finding the most appropriate CWE for a specific issue (e.g., a CVE record). Example: tool developers, security researchers. For users who wish to see all available information for the CWE/CAPEC entry. For users who want to customize what details are displayed.×
Edit Custom Filter
authentification An alternate term is "authentification", which appears to be most commonly used by people from non-English-speaking countries.AuthN "AuthN" is typically used as an abbreviation of "authentication" within the web application security community. It is also distinct from "AuthZ," which is an abbreviation of "authorization." The use of "Auth" as an abbreviation is discouraged, since it could be used for either authentication or authorization.AuthC "AuthC" is used as an abbreviation of "authentication," but it appears to used less frequently than "AuthN." This table specifies different individual consequences
associated with the weakness. The Scope identifies the application security area that is
violated, while the Impact describes the negative technical impact that arises if an
adversary succeeds in exploiting this weakness. The Likelihood provides information about
how likely the specific consequence is expected to be seen relative to the other
consequences in the list. For example, there may be high likelihood that a weakness will be
exploited to achieve a certain impact, but a low likelihood that it will be exploited to
achieve a different impact.
This table specifies different individual consequences
associated with the weakness. The Scope identifies the application security area that is
violated, while the Impact describes the negative technical impact that arises if an
adversary succeeds in exploiting this weakness. The Likelihood provides information about
how likely the specific consequence is expected to be seen relative to the other
consequences in the list. For example, there may be high likelihood that a weakness will be
exploited to achieve a certain impact, but a low likelihood that it will be exploited to
achieve a different impact.
Impact Details Read Application Data; Gain Privileges or Assume Identity; Execute Unauthorized Code or Commands
Scope: Integrity, Confidentiality, Availability, Access Control This weakness can lead to the exposure of resources or functionality to unintended actors, possibly providing attackers with sensitive information or even execute arbitrary code.Phase(s) Mitigation Architecture and Design
Strategy: Libraries or Frameworks
Use an authentication framework or library such as the OWASP ESAPI Authentication feature. This table shows the weaknesses and high level categories that are related to this
weakness. These relationships are defined as ChildOf, ParentOf, MemberOf and give insight to
similar items that may exist at higher and lower levels of abstraction. In addition,
relationships such as PeerOf and CanAlsoBe are defined to show similar weaknesses that the user
may want to explore.
This table shows the weaknesses and high level categories that are related to this
weakness. These relationships are defined as ChildOf, ParentOf, MemberOf and give insight to
similar items that may exist at higher and lower levels of abstraction. In addition,
relationships such as PeerOf and CanAlsoBe are defined to show similar weaknesses that the user
may want to explore.
 Relevant to the view "Research Concepts" (View-1000)
Relevant to the view "Research Concepts" (View-1000)
Nature Type ID Name ChildOf  Pillar - a weakness that is the most abstract type of weakness and represents a theme for all class/base/variant weaknesses related to it. A Pillar is different from a Category as a Pillar is still technically a type of weakness that describes a mistake, while a Category represents a common characteristic used to group related things.
Pillar - a weakness that is the most abstract type of weakness and represents a theme for all class/base/variant weaknesses related to it. A Pillar is different from a Category as a Pillar is still technically a type of weakness that describes a mistake, while a Category represents a common characteristic used to group related things.
284 Improper Access Control ParentOf  Base - a weakness that is still mostly independent of a resource or technology, but with sufficient details to provide specific methods for detection and prevention. Base level weaknesses typically describe issues in terms of 2 or 3 of the following dimensions: behavior, property, technology, language, and resource.
Base - a weakness that is still mostly independent of a resource or technology, but with sufficient details to provide specific methods for detection and prevention. Base level weaknesses typically describe issues in terms of 2 or 3 of the following dimensions: behavior, property, technology, language, and resource.
295 Improper Certificate Validation ParentOf  Base - a weakness that is still mostly independent of a resource or technology, but with sufficient details to provide specific methods for detection and prevention. Base level weaknesses typically describe issues in terms of 2 or 3 of the following dimensions: behavior, property, technology, language, and resource.
Base - a weakness that is still mostly independent of a resource or technology, but with sufficient details to provide specific methods for detection and prevention. Base level weaknesses typically describe issues in terms of 2 or 3 of the following dimensions: behavior, property, technology, language, and resource.
306 Missing Authentication for Critical Function ParentOf  Base - a weakness that is still mostly independent of a resource or technology, but with sufficient details to provide specific methods for detection and prevention. Base level weaknesses typically describe issues in terms of 2 or 3 of the following dimensions: behavior, property, technology, language, and resource.
Base - a weakness that is still mostly independent of a resource or technology, but with sufficient details to provide specific methods for detection and prevention. Base level weaknesses typically describe issues in terms of 2 or 3 of the following dimensions: behavior, property, technology, language, and resource.
645 Overly Restrictive Account Lockout Mechanism ParentOf  Class - a weakness that is described in a very abstract fashion, typically independent of any specific language or technology. More specific than a Pillar Weakness, but more general than a Base Weakness. Class level weaknesses typically describe issues in terms of 1 or 2 of the following dimensions: behavior, property, and resource.
Class - a weakness that is described in a very abstract fashion, typically independent of any specific language or technology. More specific than a Pillar Weakness, but more general than a Base Weakness. Class level weaknesses typically describe issues in terms of 1 or 2 of the following dimensions: behavior, property, and resource.
1390 Weak Authentication CanFollow  Base - a weakness that is still mostly independent of a resource or technology, but with sufficient details to provide specific methods for detection and prevention. Base level weaknesses typically describe issues in terms of 2 or 3 of the following dimensions: behavior, property, technology, language, and resource.
Base - a weakness that is still mostly independent of a resource or technology, but with sufficient details to provide specific methods for detection and prevention. Base level weaknesses typically describe issues in terms of 2 or 3 of the following dimensions: behavior, property, technology, language, and resource.
613 Insufficient Session Expiration  Relevant to the view "Weaknesses for Simplified Mapping of Published Vulnerabilities" (View-1003)
Relevant to the view "Weaknesses for Simplified Mapping of Published Vulnerabilities" (View-1003)
Nature Type ID Name MemberOf  View - a subset of CWE entries that provides a way of examining CWE content. The two main view structures are Slices (flat lists) and Graphs (containing relationships between entries).
View - a subset of CWE entries that provides a way of examining CWE content. The two main view structures are Slices (flat lists) and Graphs (containing relationships between entries).
1003 Weaknesses for Simplified Mapping of Published Vulnerabilities ParentOf  Base - a weakness that is still mostly independent of a resource or technology, but with sufficient details to provide specific methods for detection and prevention. Base level weaknesses typically describe issues in terms of 2 or 3 of the following dimensions: behavior, property, technology, language, and resource.
Base - a weakness that is still mostly independent of a resource or technology, but with sufficient details to provide specific methods for detection and prevention. Base level weaknesses typically describe issues in terms of 2 or 3 of the following dimensions: behavior, property, technology, language, and resource.
290 Authentication Bypass by Spoofing ParentOf  Base - a weakness that is still mostly independent of a resource or technology, but with sufficient details to provide specific methods for detection and prevention. Base level weaknesses typically describe issues in terms of 2 or 3 of the following dimensions: behavior, property, technology, language, and resource.
Base - a weakness that is still mostly independent of a resource or technology, but with sufficient details to provide specific methods for detection and prevention. Base level weaknesses typically describe issues in terms of 2 or 3 of the following dimensions: behavior, property, technology, language, and resource.
294 Authentication Bypass by Capture-replay ParentOf  Base - a weakness that is still mostly independent of a resource or technology, but with sufficient details to provide specific methods for detection and prevention. Base level weaknesses typically describe issues in terms of 2 or 3 of the following dimensions: behavior, property, technology, language, and resource.
Base - a weakness that is still mostly independent of a resource or technology, but with sufficient details to provide specific methods for detection and prevention. Base level weaknesses typically describe issues in terms of 2 or 3 of the following dimensions: behavior, property, technology, language, and resource.
295 Improper Certificate Validation ParentOf  Base - a weakness that is still mostly independent of a resource or technology, but with sufficient details to provide specific methods for detection and prevention. Base level weaknesses typically describe issues in terms of 2 or 3 of the following dimensions: behavior, property, technology, language, and resource.
Base - a weakness that is still mostly independent of a resource or technology, but with sufficient details to provide specific methods for detection and prevention. Base level weaknesses typically describe issues in terms of 2 or 3 of the following dimensions: behavior, property, technology, language, and resource.
306 Missing Authentication for Critical Function ParentOf  Base - a weakness that is still mostly independent of a resource or technology, but with sufficient details to provide specific methods for detection and prevention. Base level weaknesses typically describe issues in terms of 2 or 3 of the following dimensions: behavior, property, technology, language, and resource.
Base - a weakness that is still mostly independent of a resource or technology, but with sufficient details to provide specific methods for detection and prevention. Base level weaknesses typically describe issues in terms of 2 or 3 of the following dimensions: behavior, property, technology, language, and resource.
307 Improper Restriction of Excessive Authentication Attempts ParentOf  Base - a weakness that is still mostly independent of a resource or technology, but with sufficient details to provide specific methods for detection and prevention. Base level weaknesses typically describe issues in terms of 2 or 3 of the following dimensions: behavior, property, technology, language, and resource.
Base - a weakness that is still mostly independent of a resource or technology, but with sufficient details to provide specific methods for detection and prevention. Base level weaknesses typically describe issues in terms of 2 or 3 of the following dimensions: behavior, property, technology, language, and resource.
521 Weak Password Requirements ParentOf  Class - a weakness that is described in a very abstract fashion, typically independent of any specific language or technology. More specific than a Pillar Weakness, but more general than a Base Weakness. Class level weaknesses typically describe issues in terms of 1 or 2 of the following dimensions: behavior, property, and resource.
Class - a weakness that is described in a very abstract fashion, typically independent of any specific language or technology. More specific than a Pillar Weakness, but more general than a Base Weakness. Class level weaknesses typically describe issues in terms of 1 or 2 of the following dimensions: behavior, property, and resource.
522 Insufficiently Protected Credentials ParentOf  Base - a weakness that is still mostly independent of a resource or technology, but with sufficient details to provide specific methods for detection and prevention. Base level weaknesses typically describe issues in terms of 2 or 3 of the following dimensions: behavior, property, technology, language, and resource.
Base - a weakness that is still mostly independent of a resource or technology, but with sufficient details to provide specific methods for detection and prevention. Base level weaknesses typically describe issues in terms of 2 or 3 of the following dimensions: behavior, property, technology, language, and resource.
640 Weak Password Recovery Mechanism for Forgotten Password ParentOf  Base - a weakness that is still mostly independent of a resource or technology, but with sufficient details to provide specific methods for detection and prevention. Base level weaknesses typically describe issues in terms of 2 or 3 of the following dimensions: behavior, property, technology, language, and resource.
Base - a weakness that is still mostly independent of a resource or technology, but with sufficient details to provide specific methods for detection and prevention. Base level weaknesses typically describe issues in terms of 2 or 3 of the following dimensions: behavior, property, technology, language, and resource.
798 Use of Hard-coded Credentials  Relevant to the view "Architectural Concepts" (View-1008)
Relevant to the view "Architectural Concepts" (View-1008)
Nature Type ID Name MemberOf  Category - a CWE entry that contains a set of other entries that share a common characteristic.
Category - a CWE entry that contains a set of other entries that share a common characteristic.
1010 Authenticate Actors  Relevant to the view "CISQ Data Protection Measures" (View-1340)
Relevant to the view "CISQ Data Protection Measures" (View-1340)
Nature Type ID Name ChildOf  Pillar - a weakness that is the most abstract type of weakness and represents a theme for all class/base/variant weaknesses related to it. A Pillar is different from a Category as a Pillar is still technically a type of weakness that describes a mistake, while a Category represents a common characteristic used to group related things.
Pillar - a weakness that is the most abstract type of weakness and represents a theme for all class/base/variant weaknesses related to it. A Pillar is different from a Category as a Pillar is still technically a type of weakness that describes a mistake, while a Category represents a common characteristic used to group related things.
284 Improper Access Control  The different Modes of Introduction provide information
about how and when this
weakness may be introduced. The Phase identifies a point in the life cycle at which
introduction
may occur, while the Note provides a typical scenario related to introduction during the
given
phase.
The different Modes of Introduction provide information
about how and when this
weakness may be introduced. The Phase identifies a point in the life cycle at which
introduction
may occur, while the Note provides a typical scenario related to introduction during the
given
phase.
Phase Note Architecture and Design Implementation REALIZATION: This weakness is caused during implementation of an architectural security tactic.  This listing shows possible areas for which the given
weakness could appear. These
may be for specific named Languages, Operating Systems, Architectures, Paradigms,
Technologies,
or a class of such platforms. The platform is listed along with how frequently the given
weakness appears for that instance.
This listing shows possible areas for which the given
weakness could appear. These
may be for specific named Languages, Operating Systems, Architectures, Paradigms,
Technologies,
or a class of such platforms. The platform is listed along with how frequently the given
weakness appears for that instance.
Languages Class: Not Language-Specific (Undetermined Prevalence)
Operating Systems Class: Not OS-Specific (Undetermined Prevalence)
Technologies Class: Not Technology-Specific (Undetermined Prevalence)
Class: Web Based (Undetermined Prevalence)
Class: ICS/OT (Often Prevalent)
Example 1
The following code intends to ensure that the user is already logged in. If not, the code performs authentication with the user-provided username and password. If successful, it sets the loggedin and user cookies to "remember" that the user has already logged in. Finally, the code performs administrator tasks if the logged-in user has the "Administrator" username, as recorded in the user cookie.
(bad code)Example Language: Perlmy $q = new CGI;
if ($q->cookie('loggedin') ne "true") {}if (! AuthenticateUser($q->param('username'), $q->param('password'))) {ExitError("Error: you need to log in first");}
else {}# Set loggedin and user cookies.
$q->cookie(-name => 'loggedin',
-value => 'true'
);
$q->cookie(-name => 'user',
-value => $q->param('username')
);
if ($q->cookie('user') eq "Administrator") {DoAdministratorTasks();}Unfortunately, this code can be bypassed. The attacker can set the cookies independently so that the code does not check the username and password. The attacker could do this with an HTTP request containing headers such as:
(attack code)GET /cgi-bin/vulnerable.cgi HTTP/1.1
Cookie: user=Administrator
Cookie: loggedin=true
[body of request]By setting the loggedin cookie to "true", the attacker bypasses the entire authentication check. By using the "Administrator" value in the user cookie, the attacker also gains privileges to administer the software.
Example 2
In January 2009, an attacker was able to gain administrator access to a Twitter server because the server did not restrict the number of login attempts [REF-236]. The attacker targeted a member of Twitter's support team and was able to successfully guess the member's password using a brute force attack by guessing a large number of common words. After gaining access as the member of the support staff, the attacker used the administrator panel to gain access to 33 accounts that belonged to celebrities and politicians. Ultimately, fake Twitter messages were sent that appeared to come from the compromised accounts.
Example 2 References: [REF-236] Kim Zetter. "Weak Password Brings 'Happiness' to Twitter Hacker". 2009-01-09. <https://www.wired.com/2009/01/professed-twitt/>. URL validated: 2023-04-07.
Example 3
In 2022, the OT:ICEFALL study examined products by 10 different Operational Technology (OT) vendors. The researchers reported 56 vulnerabilities and said that the products were "insecure by design" [REF-1283]. If exploited, these vulnerabilities often allowed adversaries to change how the products operated, ranging from denial of service to changing the code that the products executed. Since these products were often used in industries such as power, electrical, water, and others, there could even be safety implications.
Multiple vendors did not use any authentication or used client-side authentication for critical functionality in their OT products.
Note: this is a curated list of examples for users to understand the variety of ways in which this weakness can be introduced. It is not a complete list of all CVEs that are related to this CWE entry.
Reference Description File-sharing PHP product does not check if user is logged in during requests for PHP library files under an includes/ directory, allowing configuration changes, code execution, and other impacts.Chat application skips validation when Central Authentication Service (CAS) is enabled, effectively removing the second factor from two-factor authenticationPython-based authentication proxy does not enforce password authentication during the initial handshake, allowing the client to bypass authentication by specifying a 'None' authentication type.TCP-based protocol in Programmable Logic Controller (PLC) has no authentication.Condition Monitor uses a protocol that does not require authentication.Safety Instrumented System uses proprietary TCP protocols with no authentication.Distributed Control System (DCS) uses a protocol that has no authentication.SCADA system only uses client-side authentication, allowing adversaries to impersonate other users.IT management product does not perform authentication for some REST API requests, as exploited in the wild per CISA KEV.Firmware for a WiFi router uses a hard-coded password for a BusyBox shell, allowing bypass of authentication through the UART portBluetooth speaker does not require authentication for the debug functionality on the UART port, allowing root shell accessDefault setting in workflow management product allows all API requests without authentication, as exploited in the wild per CISA KEV.Stack-based buffer overflows in SFK for wifi chipset used for IoT/embedded devices, as exploited in the wild per CISA KEV.Mail server does not properly check an access token before executing a Powershell command, as exploited in the wild per CISA KEV.Authentication bypass by appending specific parameters and values to a URI, as exploited in the wild per CISA KEV.Mail server does not generate a unique key during installation, as exploited in the wild per CISA KEV.LDAP Go package allows authentication bypass using an empty password, causing an unauthenticated LDAP bindlogin script for guestbook allows bypassing authentication by setting a "login_ok" parameter to 1.admin script allows authentication bypass by setting a cookie value to "LOGGEDIN".VOIP product allows authentication bypass using 127.0.0.1 in the Host header.product uses default "Allow" action, instead of default deny, leading to authentication bypass.chain: redirect without exit (CWE-698) leads to resultant authentication bypass.product does not restrict access to a listening port for a critical service, allowing authentication to be bypassed.product does not properly implement a security-related configuration setting, allowing authentication bypass.authentication routine returns "nil" instead of "false" in some situations, allowing authentication bypass using an invalid username.authentication update script does not properly handle when admin does not select any authentication modules, allowing authentication bypass.use of LDAP authentication with anonymous binds causes empty password to result in successful authenticationproduct authentication succeeds if user-provided MD5 hash matches the hash in its database; this can be subjected to replay attacks.chain: product generates predictable MD5 hashes using a constant value combined with username, allowing authentication bypass.Ordinality Description Primary(where the weakness exists independent of other weaknesses)Resultant(where the weakness is typically related to the presence of some other weaknesses)Method Details Automated Static Analysis
Automated static analysis is useful for detecting certain types of authentication. A tool may be able to analyze related configuration files, such as .htaccess in Apache web servers, or detect the usage of commonly-used authentication libraries.
Generally, automated static analysis tools have difficulty detecting custom authentication schemes. In addition, the software's design may include some functionality that is accessible to any user and does not require an established identity; an automated technique that detects the absence of authentication may report false positives.
Effectiveness: Limited
Manual Static Analysis
This weakness can be detected using tools and techniques that require manual (human) analysis, such as penetration testing, threat modeling, and interactive tools that allow the tester to record and modify an active session.
Manual static analysis is useful for evaluating the correctness of custom authentication mechanisms.
Effectiveness: High
Note:These may be more effective than strictly automated techniques. This is especially the case with weaknesses that are related to design and business rules.Manual Static Analysis - Binary or Bytecode
According to SOAR [REF-1479], the following detection techniques may be useful:
Cost effective for partial coverage:- Binary / Bytecode disassembler - then use manual analysis for vulnerabilities & anomalies
Effectiveness: SOAR Partial
Dynamic Analysis with Automated Results Interpretation
According to SOAR [REF-1479], the following detection techniques may be useful:
Cost effective for partial coverage:- Web Application Scanner
- Web Services Scanner
- Database Scanners
Effectiveness: SOAR Partial
Dynamic Analysis with Manual Results Interpretation
According to SOAR [REF-1479], the following detection techniques may be useful:
Cost effective for partial coverage:- Fuzz Tester
- Framework-based Fuzzer
Effectiveness: SOAR Partial
Manual Static Analysis - Source Code
According to SOAR [REF-1479], the following detection techniques may be useful:
Cost effective for partial coverage:- Manual Source Code Review (not inspections)
Effectiveness: SOAR Partial
Automated Static Analysis - Source Code
According to SOAR [REF-1479], the following detection techniques may be useful:
Cost effective for partial coverage:- Source code Weakness Analyzer
- Context-configured Source Code Weakness Analyzer
Effectiveness: SOAR Partial
Automated Static Analysis
According to SOAR [REF-1479], the following detection techniques may be useful:
Cost effective for partial coverage:- Configuration Checker
Effectiveness: SOAR Partial
Architecture or Design Review
According to SOAR [REF-1479], the following detection techniques may be useful:
Highly cost effective:- Inspection (IEEE 1028 standard) (can apply to requirements, design, source code, etc.)
- Formal Methods / Correct-By-Construction
Effectiveness: High
 This MemberOf Relationships table shows additional CWE Categories and Views that
reference this weakness as a member. This information is often useful in understanding where a
weakness fits within the context of external information sources.
This MemberOf Relationships table shows additional CWE Categories and Views that
reference this weakness as a member. This information is often useful in understanding where a
weakness fits within the context of external information sources.
Nature Type ID Name MemberOf  View - a subset of CWE entries that provides a way of examining CWE content. The two main view structures are Slices (flat lists) and Graphs (containing relationships between entries).
View - a subset of CWE entries that provides a way of examining CWE content. The two main view structures are Slices (flat lists) and Graphs (containing relationships between entries).635 Weaknesses Originally Used by NVD from 2008 to 2016 MemberOf  Category - a CWE entry that contains a set of other entries that share a common characteristic.
Category - a CWE entry that contains a set of other entries that share a common characteristic.718 OWASP Top Ten 2007 Category A7 - Broken Authentication and Session Management MemberOf  Category - a CWE entry that contains a set of other entries that share a common characteristic.
Category - a CWE entry that contains a set of other entries that share a common characteristic.724 OWASP Top Ten 2004 Category A3 - Broken Authentication and Session Management MemberOf  Category - a CWE entry that contains a set of other entries that share a common characteristic.
Category - a CWE entry that contains a set of other entries that share a common characteristic.812 OWASP Top Ten 2010 Category A3 - Broken Authentication and Session Management MemberOf  Category - a CWE entry that contains a set of other entries that share a common characteristic.
Category - a CWE entry that contains a set of other entries that share a common characteristic.930 OWASP Top Ten 2013 Category A2 - Broken Authentication and Session Management MemberOf  Category - a CWE entry that contains a set of other entries that share a common characteristic.
Category - a CWE entry that contains a set of other entries that share a common characteristic.947 SFP Secondary Cluster: Authentication Bypass MemberOf  Category - a CWE entry that contains a set of other entries that share a common characteristic.
Category - a CWE entry that contains a set of other entries that share a common characteristic.1028 OWASP Top Ten 2017 Category A2 - Broken Authentication MemberOf  View - a subset of CWE entries that provides a way of examining CWE content. The two main view structures are Slices (flat lists) and Graphs (containing relationships between entries).
View - a subset of CWE entries that provides a way of examining CWE content. The two main view structures are Slices (flat lists) and Graphs (containing relationships between entries).1200 Weaknesses in the 2019 CWE Top 25 Most Dangerous Software Errors MemberOf  View - a subset of CWE entries that provides a way of examining CWE content. The two main view structures are Slices (flat lists) and Graphs (containing relationships between entries).
View - a subset of CWE entries that provides a way of examining CWE content. The two main view structures are Slices (flat lists) and Graphs (containing relationships between entries).1337 Weaknesses in the 2021 CWE Top 25 Most Dangerous Software Weaknesses MemberOf  View - a subset of CWE entries that provides a way of examining CWE content. The two main view structures are Slices (flat lists) and Graphs (containing relationships between entries).
View - a subset of CWE entries that provides a way of examining CWE content. The two main view structures are Slices (flat lists) and Graphs (containing relationships between entries).1350 Weaknesses in the 2020 CWE Top 25 Most Dangerous Software Weaknesses MemberOf  Category - a CWE entry that contains a set of other entries that share a common characteristic.
Category - a CWE entry that contains a set of other entries that share a common characteristic.1353 OWASP Top Ten 2021 Category A07:2021 - Identification and Authentication Failures MemberOf  Category - a CWE entry that contains a set of other entries that share a common characteristic.
Category - a CWE entry that contains a set of other entries that share a common characteristic.1364 ICS Communications: Zone Boundary Failures MemberOf  Category - a CWE entry that contains a set of other entries that share a common characteristic.
Category - a CWE entry that contains a set of other entries that share a common characteristic.1368 ICS Dependencies (& Architecture): External Digital Systems MemberOf  View - a subset of CWE entries that provides a way of examining CWE content. The two main view structures are Slices (flat lists) and Graphs (containing relationships between entries).
View - a subset of CWE entries that provides a way of examining CWE content. The two main view structures are Slices (flat lists) and Graphs (containing relationships between entries).1387 Weaknesses in the 2022 CWE Top 25 Most Dangerous Software Weaknesses MemberOf  Category - a CWE entry that contains a set of other entries that share a common characteristic.
Category - a CWE entry that contains a set of other entries that share a common characteristic.1396 Comprehensive Categorization: Access Control MemberOf  View - a subset of CWE entries that provides a way of examining CWE content. The two main view structures are Slices (flat lists) and Graphs (containing relationships between entries).
View - a subset of CWE entries that provides a way of examining CWE content. The two main view structures are Slices (flat lists) and Graphs (containing relationships between entries).1425 Weaknesses in the 2023 CWE Top 25 Most Dangerous Software Weaknesses MemberOf  View - a subset of CWE entries that provides a way of examining CWE content. The two main view structures are Slices (flat lists) and Graphs (containing relationships between entries).
View - a subset of CWE entries that provides a way of examining CWE content. The two main view structures are Slices (flat lists) and Graphs (containing relationships between entries).1430 Weaknesses in the 2024 CWE Top 25 Most Dangerous Software Weaknesses MemberOf  Category - a CWE entry that contains a set of other entries that share a common characteristic.
Category - a CWE entry that contains a set of other entries that share a common characteristic.1442 OWASP Top Ten 2025 Category A07:2025 - Authentication Failures Usage DISCOURAGED (this CWE ID should not be used to map to real-world vulnerabilities)Reason Frequent Misuse Rationale
This CWE entry might be misused when lower-level CWE entries are likely to be applicable. It is a level-1 Class (i.e., a child of a Pillar). Comments
Consider children or descendants, beginning with CWE-1390: Weak Authentication or CWE-306: Missing Authentication for Critical Function. Suggestions
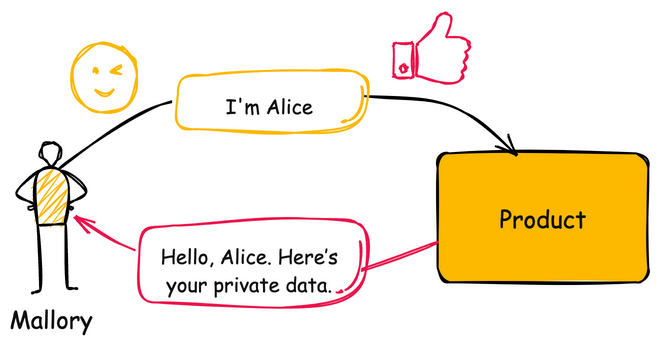
Mapped Taxonomy Name Node ID Fit Mapped Node Name PLOVER Authentication Error OWASP Top Ten 2007 A7 CWE More Specific Broken Authentication and Session Management OWASP Top Ten 2004 A3 CWE More Specific Broken Authentication and Session Management WASC 1 Insufficient Authentication ISA/IEC 62443 Part 3-3 Req SR 1.1 ISA/IEC 62443 Part 3-3 Req SR 1.2 ISA/IEC 62443 Part 4-2 Req CR 1.1 ISA/IEC 62443 Part 4-2 Req CR 1.2 CAPEC-ID Attack Pattern Name CAPEC-114 Authentication Abuse CAPEC-115 Authentication Bypass CAPEC-151 Identity Spoofing CAPEC-194 Fake the Source of Data CAPEC-22 Exploiting Trust in Client CAPEC-57 Utilizing REST's Trust in the System Resource to Obtain Sensitive Data CAPEC-593 Session Hijacking CAPEC-633 Token Impersonation CAPEC-650 Upload a Web Shell to a Web Server CAPEC-94 Adversary in the Middle (AiTM) [REF-236] Kim Zetter. "Weak Password Brings 'Happiness' to Twitter Hacker". 2009-01-09.
<https://www.wired.com/2009/01/professed-twitt/>. (URL validated: 2023-04-07)[REF-237] OWASP. "Top 10 2007-Broken Authentication and Session Management". 2007.
<https://web.archive.org/web/20160319231145/http://www.owasp.org/index.php/Top_10_2007-A7>. (URL validated: 2025-08-04)[REF-238] OWASP. "Guide to Authentication".
<http://www.owasp.org/index.php/Guide_to_Authentication>.[REF-239] Microsoft. "Authentication".
<http://msdn.microsoft.com/en-us/library/aa374735(VS.85).aspx>.[REF-7] Michael Howard and David LeBlanc. "Writing Secure Code". Chapter 4, "Authentication" Page 109. 2nd Edition. Microsoft Press. 2002-12-04.
<https://www.microsoftpressstore.com/store/writing-secure-code-9780735617223>.[REF-1283] Forescout Vedere Labs. "OT:ICEFALL: The legacy of "insecure by design" and its implications for certifications and risk management". 2022-06-20.
<https://www.forescout.com/resources/ot-icefall-report/>.More information is available — Please edit the custom filter or select a different filter.Page Last Updated: January 21, 2026Use of the Common Weakness Enumeration (CWE™) and the associated references from this website are subject to the Terms of Use. CWE is sponsored by the U.S. Department of Homeland Security (DHS) Cybersecurity and Infrastructure Security Agency (CISA) and managed by the Homeland Security Systems Engineering and Development Institute (HSSEDI) which is operated by The MITRE Corporation (MITRE). Copyright © 2006–2026, The MITRE Corporation. CWE, CWSS, CWRAF, and the CWE logo are trademarks of The MITRE Corporation.