- Home
-
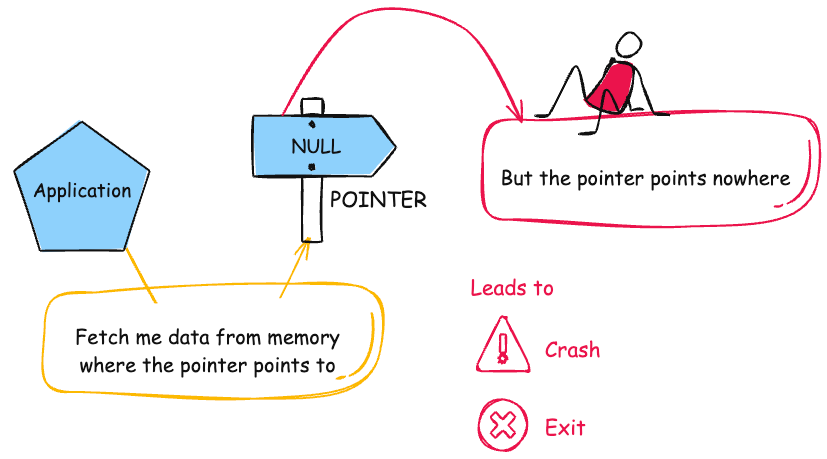
CWE-476: NULL Pointer Dereference
Weakness ID: 476Vulnerability Mapping: ALLOWED This CWE ID may be used to map to real-world vulnerabilities
Abstraction: Base Base - a weakness that is still mostly independent of a resource or technology, but with sufficient details to provide specific methods for detection and prevention. Base level weaknesses typically describe issues in terms of 2 or 3 of the following dimensions: behavior, property, technology, language, and resource.View customized information:For users who are interested in more notional aspects of a weakness. Example: educators, technical writers, and project/program managers. For users who are concerned with the practical application and details about the nature of a weakness and how to prevent it from happening. Example: tool developers, security researchers, pen-testers, incident response analysts. For users who are mapping an issue to CWE/CAPEC IDs, i.e., finding the most appropriate CWE for a specific issue (e.g., a CVE record). Example: tool developers, security researchers. For users who wish to see all available information for the CWE/CAPEC entry. For users who want to customize what details are displayed.×
Edit Custom Filter
NPD Common abbreviation for Null Pointer Dereferencenull deref Common abbreviation for Null Pointer DereferenceNPE Common abbreviation for Null Pointer Exceptionnil pointer dereference used for access of nil in Go programs This table specifies different individual consequences
associated with the weakness. The Scope identifies the application security area that is
violated, while the Impact describes the negative technical impact that arises if an
adversary succeeds in exploiting this weakness. The Likelihood provides information about
how likely the specific consequence is expected to be seen relative to the other
consequences in the list. For example, there may be high likelihood that a weakness will be
exploited to achieve a certain impact, but a low likelihood that it will be exploited to
achieve a different impact.
This table specifies different individual consequences
associated with the weakness. The Scope identifies the application security area that is
violated, while the Impact describes the negative technical impact that arises if an
adversary succeeds in exploiting this weakness. The Likelihood provides information about
how likely the specific consequence is expected to be seen relative to the other
consequences in the list. For example, there may be high likelihood that a weakness will be
exploited to achieve a certain impact, but a low likelihood that it will be exploited to
achieve a different impact.
Impact Details DoS: Crash, Exit, or Restart
Scope: Availability NULL pointer dereferences usually result in the failure of the process unless exception handling (on some platforms) is available and implemented. Even when exception handling is being used, it can still be very difficult to return the software to a safe state of operation.Execute Unauthorized Code or Commands; Read Memory; Modify Memory
Scope: Integrity, Confidentiality In rare circumstances, when NULL is equivalent to the 0x0 memory address and privileged code can access it, then writing or reading memory is possible, which may lead to code execution.Phase(s) Mitigation Implementation
For any pointers that could have been modified or provided from a function that can return NULL, check the pointer for NULL before use. When working with a multithreaded or otherwise asynchronous environment, ensure that proper locking APIs are used to lock before the check, and unlock when it has finished [REF-1484].Requirements
Select a programming language that is not susceptible to these issues.Implementation
Check the results of all functions that return a value and verify that the value is non-null before acting upon it.Effectiveness: Moderate
Architecture and Design
Identify all variables and data stores that receive information from external sources, and apply input validation to make sure that they are only initialized to expected values.Implementation
Explicitly initialize all variables and other data stores, either during declaration or just before the first usage. This table shows the weaknesses and high level categories that are related to this
weakness. These relationships are defined as ChildOf, ParentOf, MemberOf and give insight to
similar items that may exist at higher and lower levels of abstraction. In addition,
relationships such as PeerOf and CanAlsoBe are defined to show similar weaknesses that the user
may want to explore.
This table shows the weaknesses and high level categories that are related to this
weakness. These relationships are defined as ChildOf, ParentOf, MemberOf and give insight to
similar items that may exist at higher and lower levels of abstraction. In addition,
relationships such as PeerOf and CanAlsoBe are defined to show similar weaknesses that the user
may want to explore.
 Relevant to the view "Research Concepts" (View-1000)
Relevant to the view "Research Concepts" (View-1000)
Nature Type ID Name ChildOf  Pillar - a weakness that is the most abstract type of weakness and represents a theme for all class/base/variant weaknesses related to it. A Pillar is different from a Category as a Pillar is still technically a type of weakness that describes a mistake, while a Category represents a common characteristic used to group related things.
Pillar - a weakness that is the most abstract type of weakness and represents a theme for all class/base/variant weaknesses related to it. A Pillar is different from a Category as a Pillar is still technically a type of weakness that describes a mistake, while a Category represents a common characteristic used to group related things.
710 Improper Adherence to Coding Standards ChildOf  Class - a weakness that is described in a very abstract fashion, typically independent of any specific language or technology. More specific than a Pillar Weakness, but more general than a Base Weakness. Class level weaknesses typically describe issues in terms of 1 or 2 of the following dimensions: behavior, property, and resource.
Class - a weakness that is described in a very abstract fashion, typically independent of any specific language or technology. More specific than a Pillar Weakness, but more general than a Base Weakness. Class level weaknesses typically describe issues in terms of 1 or 2 of the following dimensions: behavior, property, and resource.
754 Improper Check for Unusual or Exceptional Conditions CanFollow  Base - a weakness that is still mostly independent of a resource or technology, but with sufficient details to provide specific methods for detection and prevention. Base level weaknesses typically describe issues in terms of 2 or 3 of the following dimensions: behavior, property, technology, language, and resource.
Base - a weakness that is still mostly independent of a resource or technology, but with sufficient details to provide specific methods for detection and prevention. Base level weaknesses typically describe issues in terms of 2 or 3 of the following dimensions: behavior, property, technology, language, and resource.
252 Unchecked Return Value CanFollow  Class - a weakness that is described in a very abstract fashion, typically independent of any specific language or technology. More specific than a Pillar Weakness, but more general than a Base Weakness. Class level weaknesses typically describe issues in terms of 1 or 2 of the following dimensions: behavior, property, and resource.
Class - a weakness that is described in a very abstract fashion, typically independent of any specific language or technology. More specific than a Pillar Weakness, but more general than a Base Weakness. Class level weaknesses typically describe issues in terms of 1 or 2 of the following dimensions: behavior, property, and resource.
362 Concurrent Execution using Shared Resource with Improper Synchronization ('Race Condition') CanFollow  Variant - a weakness that is linked to a certain type of product, typically involving a specific language or technology. More specific than a Base weakness. Variant level weaknesses typically describe issues in terms of 3 to 5 of the following dimensions: behavior, property, technology, language, and resource.
Variant - a weakness that is linked to a certain type of product, typically involving a specific language or technology. More specific than a Base weakness. Variant level weaknesses typically describe issues in terms of 3 to 5 of the following dimensions: behavior, property, technology, language, and resource.
789 Memory Allocation with Excessive Size Value CanFollow  Base - a weakness that is still mostly independent of a resource or technology, but with sufficient details to provide specific methods for detection and prevention. Base level weaknesses typically describe issues in terms of 2 or 3 of the following dimensions: behavior, property, technology, language, and resource.
Base - a weakness that is still mostly independent of a resource or technology, but with sufficient details to provide specific methods for detection and prevention. Base level weaknesses typically describe issues in terms of 2 or 3 of the following dimensions: behavior, property, technology, language, and resource.
1325 Improperly Controlled Sequential Memory Allocation  Relevant to the view "Software Development" (View-699)
Relevant to the view "Software Development" (View-699)
Nature Type ID Name MemberOf  Category - a CWE entry that contains a set of other entries that share a common characteristic.
Category - a CWE entry that contains a set of other entries that share a common characteristic.
465 Pointer Issues  Relevant to the view "Weaknesses for Simplified Mapping of Published Vulnerabilities" (View-1003)
Relevant to the view "Weaknesses for Simplified Mapping of Published Vulnerabilities" (View-1003)
Nature Type ID Name ChildOf  Class - a weakness that is described in a very abstract fashion, typically independent of any specific language or technology. More specific than a Pillar Weakness, but more general than a Base Weakness. Class level weaknesses typically describe issues in terms of 1 or 2 of the following dimensions: behavior, property, and resource.
Class - a weakness that is described in a very abstract fashion, typically independent of any specific language or technology. More specific than a Pillar Weakness, but more general than a Base Weakness. Class level weaknesses typically describe issues in terms of 1 or 2 of the following dimensions: behavior, property, and resource.
754 Improper Check for Unusual or Exceptional Conditions  The different Modes of Introduction provide information
about how and when this
weakness may be introduced. The Phase identifies a point in the life cycle at which
introduction
may occur, while the Note provides a typical scenario related to introduction during the
given
phase.
The different Modes of Introduction provide information
about how and when this
weakness may be introduced. The Phase identifies a point in the life cycle at which
introduction
may occur, while the Note provides a typical scenario related to introduction during the
given
phase.
Phase Note Implementation  This listing shows possible areas for which the given
weakness could appear. These
may be for specific named Languages, Operating Systems, Architectures, Paradigms,
Technologies,
or a class of such platforms. The platform is listed along with how frequently the given
weakness appears for that instance.
This listing shows possible areas for which the given
weakness could appear. These
may be for specific named Languages, Operating Systems, Architectures, Paradigms,
Technologies,
or a class of such platforms. The platform is listed along with how frequently the given
weakness appears for that instance.
Languages C (Undetermined Prevalence)
C++ (Undetermined Prevalence)
Java (Undetermined Prevalence)
C# (Undetermined Prevalence)
Go (Undetermined Prevalence)
Example 1
This example takes an IP address from a user, verifies that it is well formed and then looks up the hostname and copies it into a buffer.
(bad code)Example Language: Cvoid host_lookup(char *user_supplied_addr){}struct hostent *hp;
in_addr_t *addr;
char hostname[64];
in_addr_t inet_addr(const char *cp);
/*routine that ensures user_supplied_addr is in the right format for conversion */
validate_addr_form(user_supplied_addr);
addr = inet_addr(user_supplied_addr);
hp = gethostbyaddr( addr, sizeof(struct in_addr), AF_INET);
strcpy(hostname, hp->h_name);If an attacker provides an address that appears to be well-formed, but the address does not resolve to a hostname, then the call to gethostbyaddr() will return NULL. Since the code does not check the return value from gethostbyaddr (CWE-252), a NULL pointer dereference (CWE-476) would then occur in the call to strcpy().
Note that this code is also vulnerable to a buffer overflow (CWE-119).
Example 2
In the following code, the programmer assumes that the system always has a property named "cmd" defined. If an attacker can control the program's environment so that "cmd" is not defined, the program throws a NULL pointer exception when it attempts to call the trim() method.
(bad code)Example Language: JavaString cmd = System.getProperty("cmd");
cmd = cmd.trim();
Example 3
This Android application has registered to handle a URL when sent an intent:
(bad code)Example Language: Java
...
IntentFilter filter = new IntentFilter("com.example.URLHandler.openURL");
MyReceiver receiver = new MyReceiver();
registerReceiver(receiver, filter);
...
public class UrlHandlerReceiver extends BroadcastReceiver {}@Override
public void onReceive(Context context, Intent intent) {}if("com.example.URLHandler.openURL".equals(intent.getAction())) {String URL = intent.getStringExtra("URLToOpen");
int length = URL.length();
...
}The application assumes the URL will always be included in the intent. When the URL is not present, the call to getStringExtra() will return null, thus causing a null pointer exception when length() is called.
Example 4
Consider the following example of a typical client server exchange. The HandleRequest function is intended to perform a request and use a defer to close the connection whenever the function returns.
(bad code)Example Language: Gofunc HandleRequest(client http.Client, request *http.Request) (*http.Response, error) {response, err := client.Do(request)}
defer response.Body.Close()
if err != nil {return nil, err}
...If a user supplies a malformed request or violates the client policy, the Do method can return a nil response and a non-nil err.
This HandleRequest Function evaluates the close before checking the error. A deferred call's arguments are evaluated immediately, so the defer statement panics due to a nil response.
Note: this is a curated list of examples for users to understand the variety of ways in which this weakness can be introduced. It is not a complete list of all CVEs that are related to this CWE entry.
Reference Description C++ library for LLM inference has NULL pointer dereference if a read operation failsrace condition causes a table to be corrupted if a timer activates while it is being modified, leading to resultant NULL dereference; also involves locking.large number of packets leads to NULL dereferencepacket with invalid error status value triggers NULL dereferenceChain: race condition for an argument value, possibly resulting in NULL dereferencessh component for Go allows clients to cause a denial of service (nil pointer dereference) against SSH servers.Chain: some unprivileged ioctls do not verify that a structure has been initialized before invocation, leading to NULL dereferenceChain: IP and UDP layers each track the same value with different mechanisms that can get out of sync, possibly resulting in a NULL dereferenceChain: improper initialization of memory can lead to NULL dereferenceChain: game server can access player data structures before initialization has happened leading to NULL dereferenceChain: unchecked return value can lead to NULL dereferenceSSL software allows remote attackers to cause a denial of service (crash) via a crafted SSL/TLS handshake that triggers a null dereference.Network monitor allows remote attackers to cause a denial of service (crash) via a malformed RADIUS packet that triggers a null dereference.Network monitor allows remote attackers to cause a denial of service (crash) via a malformed Q.931, which triggers a null dereference.Chat client allows remote attackers to cause a denial of service (crash) via a passive DCC request with an invalid ID number, which causes a null dereference.Server allows remote attackers to cause a denial of service (crash) via malformed requests that trigger a null dereference.OS allows remote attackers to cause a denial of service (crash from null dereference) or execute arbitrary code via a crafted request during authentication protocol selection.Game allows remote attackers to cause a denial of service (server crash) via a missing argument, which triggers a null pointer dereference.Network monitor allows remote attackers to cause a denial of service (crash) or execute arbitrary code via malformed packets that cause a NULL pointer dereference.Ordinality Description Resultant(where the weakness is typically related to the presence of some other weaknesses)NULL pointer dereferences are frequently resultant from rarely encountered error conditions and race conditions, since these are most likely to escape detection during the testing phases.Method Details Automated Dynamic Analysis
This weakness can be detected using dynamic tools and techniques that interact with the software using large test suites with many diverse inputs, such as fuzz testing (fuzzing), robustness testing, and fault injection. The software's operation may slow down, but it should not become unstable, crash, or generate incorrect results.Effectiveness: Moderate
Manual Dynamic Analysis
Identify error conditions that are not likely to occur during normal usage and trigger them. For example, run the program under low memory conditions, run with insufficient privileges or permissions, interrupt a transaction before it is completed, or disable connectivity to basic network services such as DNS. Monitor the software for any unexpected behavior. If you trigger an unhandled exception or similar error that was discovered and handled by the application's environment, it may still indicate unexpected conditions that were not handled by the application itself.Automated Static Analysis
Automated static analysis, commonly referred to as Static Application Security Testing (SAST), can find some instances of this weakness by analyzing source code (or binary/compiled code) without having to execute it. Typically, this is done by building a model of data flow and control flow, then searching for potentially-vulnerable patterns that connect "sources" (origins of input) with "sinks" (destinations where the data interacts with external components, a lower layer such as the OS, etc.)Effectiveness: High
Automated Dynamic Analysis
Use tools that are integrated during compilation to insert runtime error-checking mechanisms related to memory safety errors, such as AddressSanitizer (ASan) for C/C++ [REF-1518].Effectiveness: Moderate
Note:Crafted inputs are necessary to reach the code containing the error, such as generated by fuzzers. Also, these tools may reduce performance, and they only report the error condition - not the original mistake that led to the error. This MemberOf Relationships table shows additional CWE Categories and Views that
reference this weakness as a member. This information is often useful in understanding where a
weakness fits within the context of external information sources.
This MemberOf Relationships table shows additional CWE Categories and Views that
reference this weakness as a member. This information is often useful in understanding where a
weakness fits within the context of external information sources.
Nature Type ID Name MemberOf  Category - a CWE entry that contains a set of other entries that share a common characteristic.
Category - a CWE entry that contains a set of other entries that share a common characteristic.398 7PK - Code Quality MemberOf  Category - a CWE entry that contains a set of other entries that share a common characteristic.
Category - a CWE entry that contains a set of other entries that share a common characteristic.730 OWASP Top Ten 2004 Category A9 - Denial of Service MemberOf  Category - a CWE entry that contains a set of other entries that share a common characteristic.
Category - a CWE entry that contains a set of other entries that share a common characteristic.737 CERT C Secure Coding Standard (2008) Chapter 4 - Expressions (EXP) MemberOf  Category - a CWE entry that contains a set of other entries that share a common characteristic.
Category - a CWE entry that contains a set of other entries that share a common characteristic.742 CERT C Secure Coding Standard (2008) Chapter 9 - Memory Management (MEM) MemberOf  Category - a CWE entry that contains a set of other entries that share a common characteristic.
Category - a CWE entry that contains a set of other entries that share a common characteristic.808 2010 Top 25 - Weaknesses On the Cusp MemberOf  Category - a CWE entry that contains a set of other entries that share a common characteristic.
Category - a CWE entry that contains a set of other entries that share a common characteristic.867 2011 Top 25 - Weaknesses On the Cusp MemberOf  Category - a CWE entry that contains a set of other entries that share a common characteristic.
Category - a CWE entry that contains a set of other entries that share a common characteristic.871 CERT C++ Secure Coding Section 03 - Expressions (EXP) MemberOf  Category - a CWE entry that contains a set of other entries that share a common characteristic.
Category - a CWE entry that contains a set of other entries that share a common characteristic.876 CERT C++ Secure Coding Section 08 - Memory Management (MEM) MemberOf  View - a subset of CWE entries that provides a way of examining CWE content. The two main view structures are Slices (flat lists) and Graphs (containing relationships between entries).
View - a subset of CWE entries that provides a way of examining CWE content. The two main view structures are Slices (flat lists) and Graphs (containing relationships between entries).884 CWE Cross-section MemberOf  Category - a CWE entry that contains a set of other entries that share a common characteristic.
Category - a CWE entry that contains a set of other entries that share a common characteristic.971 SFP Secondary Cluster: Faulty Pointer Use MemberOf  Category - a CWE entry that contains a set of other entries that share a common characteristic.
Category - a CWE entry that contains a set of other entries that share a common characteristic.1136 SEI CERT Oracle Secure Coding Standard for Java - Guidelines 02. Expressions (EXP) MemberOf  Category - a CWE entry that contains a set of other entries that share a common characteristic.
Category - a CWE entry that contains a set of other entries that share a common characteristic.1157 SEI CERT C Coding Standard - Guidelines 03. Expressions (EXP) MemberOf  View - a subset of CWE entries that provides a way of examining CWE content. The two main view structures are Slices (flat lists) and Graphs (containing relationships between entries).
View - a subset of CWE entries that provides a way of examining CWE content. The two main view structures are Slices (flat lists) and Graphs (containing relationships between entries).1200 Weaknesses in the 2019 CWE Top 25 Most Dangerous Software Errors MemberOf  Category - a CWE entry that contains a set of other entries that share a common characteristic.
Category - a CWE entry that contains a set of other entries that share a common characteristic.1306 CISQ Quality Measures - Reliability MemberOf  View - a subset of CWE entries that provides a way of examining CWE content. The two main view structures are Slices (flat lists) and Graphs (containing relationships between entries).
View - a subset of CWE entries that provides a way of examining CWE content. The two main view structures are Slices (flat lists) and Graphs (containing relationships between entries).1337 Weaknesses in the 2021 CWE Top 25 Most Dangerous Software Weaknesses MemberOf  View - a subset of CWE entries that provides a way of examining CWE content. The two main view structures are Slices (flat lists) and Graphs (containing relationships between entries).
View - a subset of CWE entries that provides a way of examining CWE content. The two main view structures are Slices (flat lists) and Graphs (containing relationships between entries).1350 Weaknesses in the 2020 CWE Top 25 Most Dangerous Software Weaknesses MemberOf  View - a subset of CWE entries that provides a way of examining CWE content. The two main view structures are Slices (flat lists) and Graphs (containing relationships between entries).
View - a subset of CWE entries that provides a way of examining CWE content. The two main view structures are Slices (flat lists) and Graphs (containing relationships between entries).1387 Weaknesses in the 2022 CWE Top 25 Most Dangerous Software Weaknesses MemberOf  Category - a CWE entry that contains a set of other entries that share a common characteristic.
Category - a CWE entry that contains a set of other entries that share a common characteristic.1412 Comprehensive Categorization: Poor Coding Practices MemberOf  View - a subset of CWE entries that provides a way of examining CWE content. The two main view structures are Slices (flat lists) and Graphs (containing relationships between entries).
View - a subset of CWE entries that provides a way of examining CWE content. The two main view structures are Slices (flat lists) and Graphs (containing relationships between entries).1425 Weaknesses in the 2023 CWE Top 25 Most Dangerous Software Weaknesses MemberOf  View - a subset of CWE entries that provides a way of examining CWE content. The two main view structures are Slices (flat lists) and Graphs (containing relationships between entries).
View - a subset of CWE entries that provides a way of examining CWE content. The two main view structures are Slices (flat lists) and Graphs (containing relationships between entries).1430 Weaknesses in the 2024 CWE Top 25 Most Dangerous Software Weaknesses MemberOf  View - a subset of CWE entries that provides a way of examining CWE content. The two main view structures are Slices (flat lists) and Graphs (containing relationships between entries).
View - a subset of CWE entries that provides a way of examining CWE content. The two main view structures are Slices (flat lists) and Graphs (containing relationships between entries).1435 Weaknesses in the 2025 CWE Top 25 Most Dangerous Software Weaknesses MemberOf  Category - a CWE entry that contains a set of other entries that share a common characteristic.
Category - a CWE entry that contains a set of other entries that share a common characteristic.1445 OWASP Top Ten 2025 Category A10:2025 - Mishandling of Exceptional Conditions Usage ALLOWED (this CWE ID may be used to map to real-world vulnerabilities)Reason Acceptable-Use Rationale
This CWE entry is at the Base level of abstraction, which is a preferred level of abstraction for mapping to the root causes of vulnerabilities. Comments
Carefully read both the name and description to ensure that this mapping is an appropriate fit. Do not try to 'force' a mapping to a lower-level Base/Variant simply to comply with this preferred level of abstraction. Mapped Taxonomy Name Node ID Fit Mapped Node Name 7 Pernicious Kingdoms Null Dereference CLASP Null-pointer dereference PLOVER Null Dereference (Null Pointer Dereference) OWASP Top Ten 2004 A9 CWE More Specific Denial of Service CERT C Secure Coding EXP34-C Exact Do not dereference null pointers Software Fault Patterns SFP7 Faulty Pointer Use [REF-6] Katrina Tsipenyuk, Brian Chess and Gary McGraw. "Seven Pernicious Kingdoms: A Taxonomy of Software Security Errors". NIST Workshop on Software Security Assurance Tools Techniques and Metrics. NIST. 2005-11-07.
<https://samate.nist.gov/SSATTM_Content/papers/Seven%20Pernicious%20Kingdoms%20-%20Taxonomy%20of%20Sw%20Security%20Errors%20-%20Tsipenyuk%20-%20Chess%20-%20McGraw.pdf>.[REF-18] Secure Software, Inc.. "The CLASP Application Security Process". 2005.
<https://cwe.mitre.org/documents/sources/TheCLASPApplicationSecurityProcess.pdf>. (URL validated: 2024-11-17)[REF-1031] "Null pointer / Null dereferencing". Wikipedia. 2019-07-15.
<https://en.wikipedia.org/wiki/Null_pointer#Null_dereferencing>.[REF-1032] "Null Reference Creation and Null Pointer Dereference". Apple.
<https://developer.apple.com/documentation/xcode/null-reference-creation-and-null-pointer-dereference>. (URL validated: 2023-04-07)[REF-1033] "NULL Pointer Dereference [CWE-476]". ImmuniWeb. 2012-09-11.
<https://www.immuniweb.com/vulnerability/null-pointer-dereference.html>.[REF-1484] D3FEND. "D3FEND: D3-NPC Null Pointer Checking".
<https://d3fend.mitre.org/technique/d3f:NullPointerChecking//>. (URL validated: 2025-09-08)[REF-1518] "AddressSanitizer".
<https://clang.llvm.org/docs/AddressSanitizer.html>. (URL validated: 2025-12-10)More information is available — Please edit the custom filter or select a different filter.Page Last Updated: January 21, 2026Use of the Common Weakness Enumeration (CWE™) and the associated references from this website are subject to the Terms of Use. CWE is sponsored by the U.S. Department of Homeland Security (DHS) Cybersecurity and Infrastructure Security Agency (CISA) and managed by the Homeland Security Systems Engineering and Development Institute (HSSEDI) which is operated by The MITRE Corporation (MITRE). Copyright © 2006–2026, The MITRE Corporation. CWE, CWSS, CWRAF, and the CWE logo are trademarks of The MITRE Corporation.