- Home
-
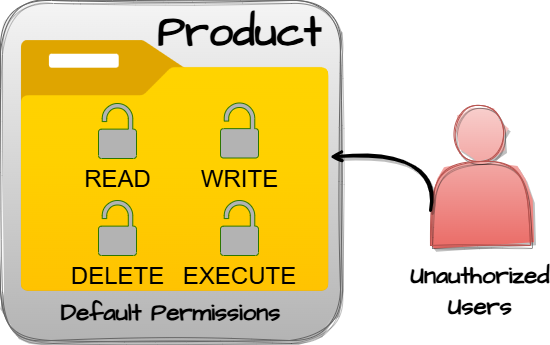
CWE-276: Incorrect Default Permissions
Weakness ID: 276Vulnerability Mapping: ALLOWED This CWE ID may be used to map to real-world vulnerabilities
Abstraction: Base Base - a weakness that is still mostly independent of a resource or technology, but with sufficient details to provide specific methods for detection and prevention. Base level weaknesses typically describe issues in terms of 2 or 3 of the following dimensions: behavior, property, technology, language, and resource.View customized information:For users who are interested in more notional aspects of a weakness. Example: educators, technical writers, and project/program managers. For users who are concerned with the practical application and details about the nature of a weakness and how to prevent it from happening. Example: tool developers, security researchers, pen-testers, incident response analysts. For users who are mapping an issue to CWE/CAPEC IDs, i.e., finding the most appropriate CWE for a specific issue (e.g., a CVE record). Example: tool developers, security researchers. For users who wish to see all available information for the CWE/CAPEC entry. For users who want to customize what details are displayed.×
Edit Custom Filter
 This table specifies different individual consequences
associated with the weakness. The Scope identifies the application security area that is
violated, while the Impact describes the negative technical impact that arises if an
adversary succeeds in exploiting this weakness. The Likelihood provides information about
how likely the specific consequence is expected to be seen relative to the other
consequences in the list. For example, there may be high likelihood that a weakness will be
exploited to achieve a certain impact, but a low likelihood that it will be exploited to
achieve a different impact.
This table specifies different individual consequences
associated with the weakness. The Scope identifies the application security area that is
violated, while the Impact describes the negative technical impact that arises if an
adversary succeeds in exploiting this weakness. The Likelihood provides information about
how likely the specific consequence is expected to be seen relative to the other
consequences in the list. For example, there may be high likelihood that a weakness will be
exploited to achieve a certain impact, but a low likelihood that it will be exploited to
achieve a different impact.
Impact Details Read Application Data; Modify Application Data
Scope: Confidentiality, Integrity Phase(s) Mitigation Architecture and Design; Operation
The architecture needs to access and modification attributes for files to only those users who actually require those actions.Architecture and Design
Strategy: Separation of Privilege
Compartmentalize the system to have "safe" areas where trust boundaries can be unambiguously drawn. Do not allow sensitive data to go outside of the trust boundary and always be careful when interfacing with a compartment outside of the safe area.
Ensure that appropriate compartmentalization is built into the system design, and the compartmentalization allows for and reinforces privilege separation functionality. Architects and designers should rely on the principle of least privilege to decide the appropriate time to use privileges and the time to drop privileges.
 This table shows the weaknesses and high level categories that are related to this
weakness. These relationships are defined as ChildOf, ParentOf, MemberOf and give insight to
similar items that may exist at higher and lower levels of abstraction. In addition,
relationships such as PeerOf and CanAlsoBe are defined to show similar weaknesses that the user
may want to explore.
This table shows the weaknesses and high level categories that are related to this
weakness. These relationships are defined as ChildOf, ParentOf, MemberOf and give insight to
similar items that may exist at higher and lower levels of abstraction. In addition,
relationships such as PeerOf and CanAlsoBe are defined to show similar weaknesses that the user
may want to explore.
 Relevant to the view "Research Concepts" (View-1000)
Relevant to the view "Research Concepts" (View-1000)
Nature Type ID Name ChildOf  Class - a weakness that is described in a very abstract fashion, typically independent of any specific language or technology. More specific than a Pillar Weakness, but more general than a Base Weakness. Class level weaknesses typically describe issues in terms of 1 or 2 of the following dimensions: behavior, property, and resource.
Class - a weakness that is described in a very abstract fashion, typically independent of any specific language or technology. More specific than a Pillar Weakness, but more general than a Base Weakness. Class level weaknesses typically describe issues in terms of 1 or 2 of the following dimensions: behavior, property, and resource.
732 Incorrect Permission Assignment for Critical Resource  Relevant to the view "Software Development" (View-699)
Relevant to the view "Software Development" (View-699)
Nature Type ID Name MemberOf  Category - a CWE entry that contains a set of other entries that share a common characteristic.
Category - a CWE entry that contains a set of other entries that share a common characteristic.
275 Permission Issues  Relevant to the view "Weaknesses for Simplified Mapping of Published Vulnerabilities" (View-1003)
Relevant to the view "Weaknesses for Simplified Mapping of Published Vulnerabilities" (View-1003)
Nature Type ID Name ChildOf  Class - a weakness that is described in a very abstract fashion, typically independent of any specific language or technology. More specific than a Pillar Weakness, but more general than a Base Weakness. Class level weaknesses typically describe issues in terms of 1 or 2 of the following dimensions: behavior, property, and resource.
Class - a weakness that is described in a very abstract fashion, typically independent of any specific language or technology. More specific than a Pillar Weakness, but more general than a Base Weakness. Class level weaknesses typically describe issues in terms of 1 or 2 of the following dimensions: behavior, property, and resource.
732 Incorrect Permission Assignment for Critical Resource  Relevant to the view "Architectural Concepts" (View-1008)
Relevant to the view "Architectural Concepts" (View-1008)
Nature Type ID Name MemberOf  Category - a CWE entry that contains a set of other entries that share a common characteristic.
Category - a CWE entry that contains a set of other entries that share a common characteristic.
1011 Authorize Actors  Relevant to the view "Hardware Design" (View-1194)
Relevant to the view "Hardware Design" (View-1194)
Nature Type ID Name MemberOf  Category - a CWE entry that contains a set of other entries that share a common characteristic.
Category - a CWE entry that contains a set of other entries that share a common characteristic.
1198 Privilege Separation and Access Control Issues  The different Modes of Introduction provide information
about how and when this
weakness may be introduced. The Phase identifies a point in the life cycle at which
introduction
may occur, while the Note provides a typical scenario related to introduction during the
given
phase.
The different Modes of Introduction provide information
about how and when this
weakness may be introduced. The Phase identifies a point in the life cycle at which
introduction
may occur, while the Note provides a typical scenario related to introduction during the
given
phase.
Phase Note Architecture and Design Implementation Installation Operation  This listing shows possible areas for which the given
weakness could appear. These
may be for specific named Languages, Operating Systems, Architectures, Paradigms,
Technologies,
or a class of such platforms. The platform is listed along with how frequently the given
weakness appears for that instance.
This listing shows possible areas for which the given
weakness could appear. These
may be for specific named Languages, Operating Systems, Architectures, Paradigms,
Technologies,
or a class of such platforms. The platform is listed along with how frequently the given
weakness appears for that instance.
Languages Class: Not Language-Specific (Undetermined Prevalence)
Technologies Class: Not Technology-Specific (Undetermined Prevalence)
Class: ICS/OT (Undetermined Prevalence)
Note: this is a curated list of examples for users to understand the variety of ways in which this weakness can be introduced. It is not a complete list of all CVEs that are related to this CWE entry.
Reference Description Executables installed world-writable.Home directories installed world-readable.World-writable log files allow information loss; world-readable file has cleartext passwords.World-readable directory.Windows product uses insecure permissions when installing on Solaris (genesis: port error).Insecure permissions for a shared secret key file. Overlaps cryptographic problem.Default permissions of a device allow IP spoofing.Ordinality Description Primary(where the weakness exists independent of other weaknesses)Method Details Automated Static Analysis - Binary or Bytecode
According to SOAR [REF-1479], the following detection techniques may be useful:
Cost effective for partial coverage:- Inter-application Flow Analysis
Effectiveness: SOAR Partial
Manual Static Analysis - Binary or Bytecode
According to SOAR [REF-1479], the following detection techniques may be useful:
Cost effective for partial coverage:- Binary / Bytecode disassembler - then use manual analysis for vulnerabilities & anomalies
Effectiveness: SOAR Partial
Dynamic Analysis with Automated Results Interpretation
According to SOAR [REF-1479], the following detection techniques may be useful:
Cost effective for partial coverage:- Host-based Vulnerability Scanners - Examine configuration for flaws, verifying that audit mechanisms work, ensure host configuration meets certain predefined criteria
- Web Application Scanner
- Web Services Scanner
- Database Scanners
Effectiveness: SOAR Partial
Dynamic Analysis with Manual Results Interpretation
According to SOAR [REF-1479], the following detection techniques may be useful:
Highly cost effective:- Host Application Interface Scanner
Cost effective for partial coverage:- Fuzz Tester
- Framework-based Fuzzer
- Automated Monitored Execution
- Forced Path Execution
Effectiveness: High
Manual Static Analysis - Source Code
According to SOAR [REF-1479], the following detection techniques may be useful:
Highly cost effective:- Manual Source Code Review (not inspections)
Cost effective for partial coverage:- Focused Manual Spotcheck - Focused manual analysis of source
Effectiveness: High
Automated Static Analysis - Source Code
According to SOAR [REF-1479], the following detection techniques may be useful:
Cost effective for partial coverage:- Context-configured Source Code Weakness Analyzer
Effectiveness: SOAR Partial
Automated Static Analysis
According to SOAR [REF-1479], the following detection techniques may be useful:
Cost effective for partial coverage:- Configuration Checker
Effectiveness: SOAR Partial
Architecture or Design Review
According to SOAR [REF-1479], the following detection techniques may be useful:
Highly cost effective:- Formal Methods / Correct-By-Construction
Cost effective for partial coverage:- Inspection (IEEE 1028 standard) (can apply to requirements, design, source code, etc.)
Effectiveness: High
 This MemberOf Relationships table shows additional CWE Categories and Views that
reference this weakness as a member. This information is often useful in understanding where a
weakness fits within the context of external information sources.
This MemberOf Relationships table shows additional CWE Categories and Views that
reference this weakness as a member. This information is often useful in understanding where a
weakness fits within the context of external information sources.
Nature Type ID Name MemberOf  Category - a CWE entry that contains a set of other entries that share a common characteristic.
Category - a CWE entry that contains a set of other entries that share a common characteristic.743 CERT C Secure Coding Standard (2008) Chapter 10 - Input Output (FIO) MemberOf  Category - a CWE entry that contains a set of other entries that share a common characteristic.
Category - a CWE entry that contains a set of other entries that share a common characteristic.857 The CERT Oracle Secure Coding Standard for Java (2011) Chapter 14 - Input Output (FIO) MemberOf  Category - a CWE entry that contains a set of other entries that share a common characteristic.
Category - a CWE entry that contains a set of other entries that share a common characteristic.877 CERT C++ Secure Coding Section 09 - Input Output (FIO) MemberOf  Category - a CWE entry that contains a set of other entries that share a common characteristic.
Category - a CWE entry that contains a set of other entries that share a common characteristic.946 SFP Secondary Cluster: Insecure Resource Permissions MemberOf  Category - a CWE entry that contains a set of other entries that share a common characteristic.
Category - a CWE entry that contains a set of other entries that share a common characteristic.1147 SEI CERT Oracle Secure Coding Standard for Java - Guidelines 13. Input Output (FIO) MemberOf  View - a subset of CWE entries that provides a way of examining CWE content. The two main view structures are Slices (flat lists) and Graphs (containing relationships between entries).
View - a subset of CWE entries that provides a way of examining CWE content. The two main view structures are Slices (flat lists) and Graphs (containing relationships between entries).1337 Weaknesses in the 2021 CWE Top 25 Most Dangerous Software Weaknesses MemberOf  Category - a CWE entry that contains a set of other entries that share a common characteristic.
Category - a CWE entry that contains a set of other entries that share a common characteristic.1345 OWASP Top Ten 2021 Category A01:2021 - Broken Access Control MemberOf  Category - a CWE entry that contains a set of other entries that share a common characteristic.
Category - a CWE entry that contains a set of other entries that share a common characteristic.1366 ICS Communications: Frail Security in Protocols MemberOf  Category - a CWE entry that contains a set of other entries that share a common characteristic.
Category - a CWE entry that contains a set of other entries that share a common characteristic.1376 ICS Engineering (Construction/Deployment): Security Gaps in Commissioning MemberOf  View - a subset of CWE entries that provides a way of examining CWE content. The two main view structures are Slices (flat lists) and Graphs (containing relationships between entries).
View - a subset of CWE entries that provides a way of examining CWE content. The two main view structures are Slices (flat lists) and Graphs (containing relationships between entries).1387 Weaknesses in the 2022 CWE Top 25 Most Dangerous Software Weaknesses MemberOf  Category - a CWE entry that contains a set of other entries that share a common characteristic.
Category - a CWE entry that contains a set of other entries that share a common characteristic.1396 Comprehensive Categorization: Access Control MemberOf  View - a subset of CWE entries that provides a way of examining CWE content. The two main view structures are Slices (flat lists) and Graphs (containing relationships between entries).
View - a subset of CWE entries that provides a way of examining CWE content. The two main view structures are Slices (flat lists) and Graphs (containing relationships between entries).1425 Weaknesses in the 2023 CWE Top 25 Most Dangerous Software Weaknesses MemberOf  Category - a CWE entry that contains a set of other entries that share a common characteristic.
Category - a CWE entry that contains a set of other entries that share a common characteristic.1436 OWASP Top Ten 2025 Category A01:2025 - Broken Access Control Usage ALLOWED (this CWE ID may be used to map to real-world vulnerabilities)Reason Acceptable-Use Rationale
This CWE entry is at the Base level of abstraction, which is a preferred level of abstraction for mapping to the root causes of vulnerabilities. Comments
Carefully read both the name and description to ensure that this mapping is an appropriate fit. Do not try to 'force' a mapping to a lower-level Base/Variant simply to comply with this preferred level of abstraction. Maintenance
As of CWE 4.19, this entry is being considered for deprecation or significant revision. Its name and description are inconsistent. The name is more general, and the description is more specific. The description emphasizes the installation phase only; mentions only files; and emphasizes modification of those files. The name applies to any type of resource, does not mention the specific permissions, and could be relevant to any SDLC phase.Mapped Taxonomy Name Node ID Fit Mapped Node Name PLOVER Insecure Default Permissions CERT C Secure Coding FIO06-C Create files with appropriate access permissions The CERT Oracle Secure Coding Standard for Java (2011) FIO01-J Create files with appropriate access permission ISA/IEC 62443 Part 2-4 Req SP.03.08 ISA/IEC 62443 Part 4-2 Req CR 2.1 [REF-62] Mark Dowd, John McDonald and Justin Schuh. "The Art of Software Security Assessment". Chapter 3, "Insecure Defaults", Page 69. 1st Edition. Addison Wesley. 2006. [REF-1479] Gregory Larsen, E. Kenneth Hong Fong, David A. Wheeler and Rama S. Moorthy. "State-of-the-Art Resources (SOAR) for Software Vulnerability Detection, Test, and Evaluation". 2014-07.
<https://www.ida.org/-/media/feature/publications/s/st/stateoftheart-resources-soar-for-software-vulnerability-detection-test-and-evaluation/p-5061.ashx>. (URL validated: 2025-09-05)[REF-1479] Gregory Larsen, E. Kenneth Hong Fong, David A. Wheeler and Rama S. Moorthy. "State-of-the-Art Resources (SOAR) for Software Vulnerability Detection, Test, and Evaluation". 2014-07.
<https://www.ida.org/-/media/feature/publications/s/st/stateoftheart-resources-soar-for-software-vulnerability-detection-test-and-evaluation/p-5061.ashx>. (URL validated: 2025-09-05)More information is available — Please edit the custom filter or select a different filter.Page Last Updated: January 21, 2026Use of the Common Weakness Enumeration (CWE™) and the associated references from this website are subject to the Terms of Use. CWE is sponsored by the U.S. Department of Homeland Security (DHS) Cybersecurity and Infrastructure Security Agency (CISA) and managed by the Homeland Security Systems Engineering and Development Institute (HSSEDI) which is operated by The MITRE Corporation (MITRE). Copyright © 2006–2026, The MITRE Corporation. CWE, CWSS, CWRAF, and the CWE logo are trademarks of The MITRE Corporation.